
Continuous Cybersecurity Validation Through the Eyes of an Attacker
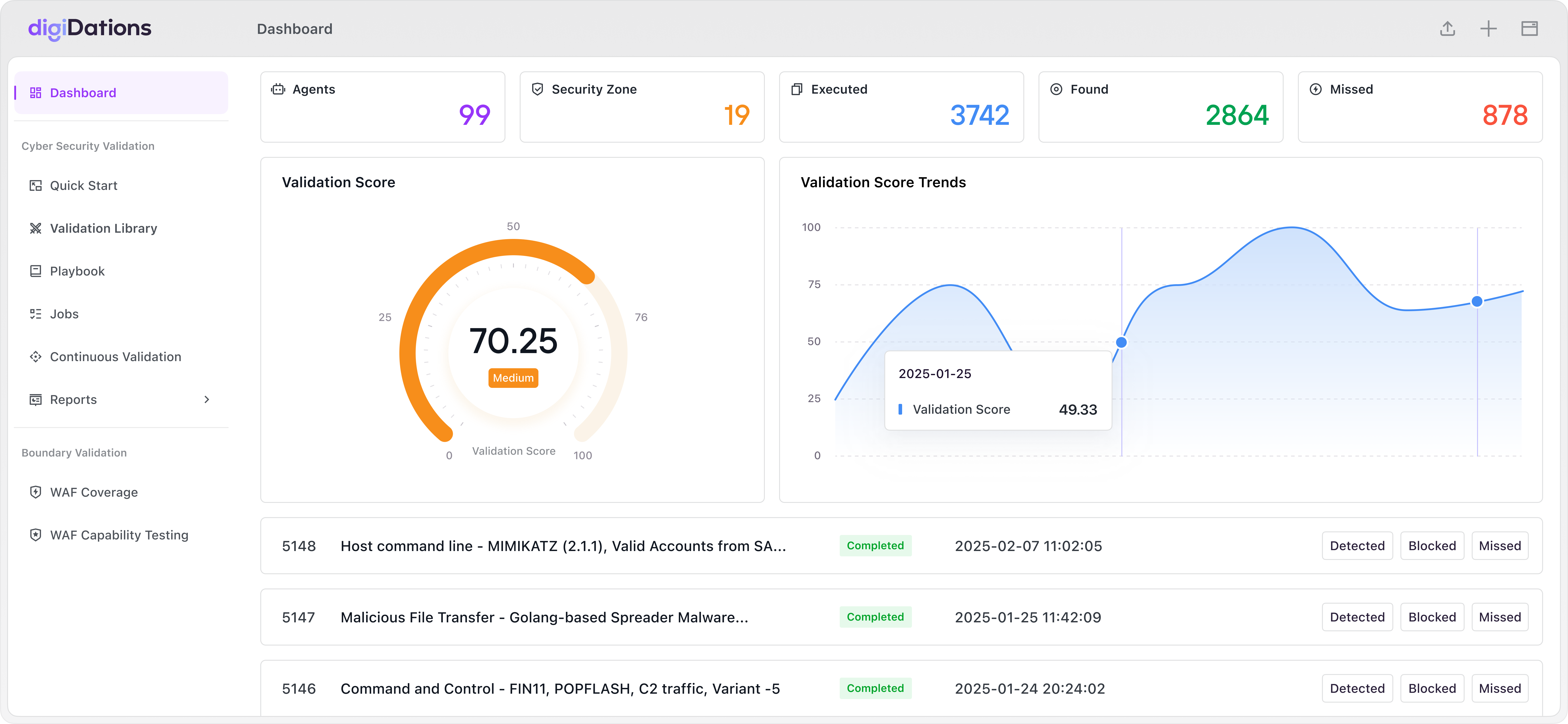
The platform delivers real-time validation of your cyber defenses by simulating attacks using TTPs. It measures the effectiveness of security controls and platforms, showing the before-and-after impact of changes.
24/7 automated cybersecurity validation
Zero business impact
Data-driven security decisions
Comprehensive security validation assurance powered by a robust, real-world attack database to evaluate your defense readiness.
0
Security Validation Rules
MITRE ATT&CK Mapped
MITRE ATT&CK Mapped
0
APT Groups Tracked
Real Attack Patterns
Real Attack Patterns
0
Attack Scenarios
Including Various Attack Campaigns
Including Various Attack Campaigns
3
SOC Efficiency Improvement
AI-Driven Automation
AI-Driven Automation
Platform
ATLAS – AI Powered Continuous Cybersecurity Validation Platform
Real-World Advanced Persistent Threat (APT) Simulation
Leverage advanced AI to simulate sophisticated cyber threats and attack patterns with comprehensive attack coverage.
Actionable Security Intelligence
& Incident Response
Transform complex security data into clear, actionable insights with comprehensive analytics and reporting.
Breach and attack simulation mapped to MITRE ATT&CK
AI-driven attack chain orchestration for realistic scenarios
Dynamic scenario adjustment based on your environment
Multi-dimensional security metrics and KPIs
Customizable executive dashboards and reports
Trend analysis and predictive insights
Methodology
Continuous Cybersecurity Validation Journey
Stage 1
VERIFY
Are our current security deployments and configurations aligned with our designs?
Validate your security configurations and baseline controls to maintain a resilient defense foundation.
Stage 2
EVALUATE
How effective are our security products in real-world attack scenarios?
Validate security controls against real-world attack scenarios to maximize protection effectiveness.
Stage 3
ANALYZE
Do our correlation rules accurately identify real threats?
Validate correlation capabilities to identify incidents from security events, improving detection accuracy and reducing alert fatigue.
Stage 4
OPTIMIZE
Will our incident response process follow the plan consistently?
Validate end-to-end incident response workflows to ensure timely and effective threat mitigation.
Deploy Your Way

On-Premise
Complete control and data sovereignty

SaaS Platform
Quick start with zero infrastructure
